Share this
Virus Alert: Beware of CTB-Locker Disguised as Windows 10 Upgrade
by Bridget.Giacinto on Aug 3, 2015 2:56:51 PM
While there are over 14 million machines and counting already running Windows 10, there are millions worldwide that are still waiting. With the long waiting list to upgrade to Windows 10, it somehow doesn’t surprise me that hackers would find a way to take advantage of that fact.
The TALOS Group, a security intelligence and research group that focuses on malware analysis just reported the discovery of a new variant of the costly crypto viruses that have plagued unsuspecting computer users over the last few years. This new variant, called CTB-Locker (also known as Critroni), is part of a new spam email campaign that is pushing this crypto ransomware disguised as a Windows 10 upgrade.
Watch for Spam Email Campaign Disguised as Windows 10 Upgrade
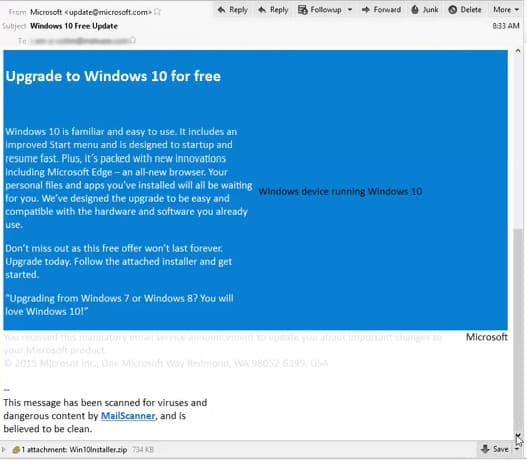
The spam email looks legitimate; it uses Microsoft colors, the footer appears to be from Microsoft and the from address of the email appears as if it is coming from Microsoft, but it is NOT actually coming from Microsoft. Hackers have been spoofing email addresses for some time now. This is just one of the ways hackers try to legitimize their emails by forging the senders address in an attempt to get you to open the email from what appears to be a trusted source.
There are tools that you can use to trace an email address to the senders IP location. A lookup of this email address revealed that the source originated from Thailand, which is suspicious.
The other thing that these hackers did to provide artificial confidence in users in order to get them to download the attachment, was to include a message at the bottom of the email that states that the email has been scanned for viruses and dangerous content. This is just another ploy to get you to take the action they want, which is to download the file that contains their crypto virus.
The email contains a zip file that appears to have the Windows 10 upgrade. The problem with this download, is that it also contains a dangerous virus that encrypts your data and holds it for ransom until you pay up.
To protect yourself, I would recommend creating an image backup of your computer prior to downloading any Windows 10 operating system, and to store it on an external, unconnected device. That way, if for any reason something goes wrong, like in the case of this virus, you can just remove the virus from your computer and then restore your entire system.
CTB Locker, The Newest Crypto Virus
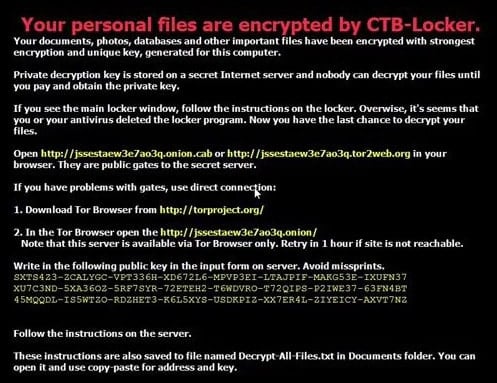
If you were to unzip this file and run the executable installation file, you would quickly learn that there is a major problem. The first message you would see lets you know that your personal files have been encrypted with CTB-Locker. Your documents, photos, databases, and other important files at this point would have been encrypted with the strongest encryption available using a unique key, generated for your specific computer.
You are also informed that the private decryption key is stored on a secret Internet server and that nobody can decrypt your files until you pay and obtain this private key.
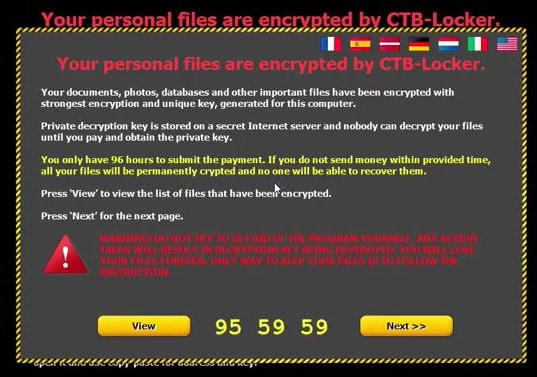
The counter immediately starts to count down the time remaining. If you have not created a backup of your data, you are not left with many options. To make matters worse, they only give you 96 hours to pay up (using Tor and Bitcoin to remain anonymous) or your data will be permanently crypted and you will NEVER be able to retrieve them.
The big take-away here is you have to back up your data to an external source. We recommend that you have multiple backups and that you rotate your backup storage devices so that you always have a secondary, unconnected backup of your data. If your backup is stored on a connected device and your backup is saved without any encryption, you run a greater risk of not being able to recover your files from your backup should this virus gain access to your computer. Any drive, including network drives could become encrypted as a result of this ransomware virus.
If you have not yet backed up your data, you can download a free trial of NovaBACKUP and create a backup now.
Share this
- Pre-Sales Questions (112)
- Tips and Tricks (95)
- Industry News (60)
- Reseller / MSP (37)
- Security Threats / Ransomware (30)
- Applications (28)
- Best Practices (27)
- Cloud Backup (25)
- Disaster Recovery (25)
- Backup Videos (24)
- Compliance / HIPAA (23)
- Storage Technology (21)
- Virtual Environments (17)
- Technology Updates / Releases (9)
- Infographics (8)
- Backup preparation (3)
- Company (US) (1)
- Events (1)
- Events (US) (1)
- Products (US) (1)
- April 2024 (1)
- March 2024 (2)
- February 2024 (2)
- January 2024 (1)
- December 2023 (1)
- November 2023 (1)
- October 2023 (1)
- September 2023 (1)
- August 2023 (1)
- July 2023 (1)
- May 2023 (1)
- March 2023 (3)
- February 2023 (2)
- January 2023 (3)
- December 2022 (1)
- November 2022 (2)
- October 2022 (2)
- September 2022 (2)
- August 2022 (2)
- July 2022 (1)
- June 2022 (1)
- April 2022 (1)
- March 2022 (2)
- February 2022 (1)
- January 2022 (1)
- December 2021 (1)
- November 2021 (1)
- September 2021 (1)
- August 2021 (1)
- July 2021 (1)
- June 2021 (2)
- May 2021 (2)
- April 2021 (1)
- March 2021 (2)
- February 2021 (1)
- January 2021 (2)
- December 2020 (1)
- November 2020 (1)
- October 2020 (2)
- September 2020 (4)
- August 2020 (2)
- July 2020 (1)
- June 2020 (1)
- May 2020 (1)
- April 2020 (1)
- March 2020 (3)
- February 2020 (2)
- January 2020 (2)
- December 2019 (1)
- November 2019 (1)
- October 2019 (1)
- August 2019 (1)
- July 2019 (1)
- June 2019 (1)
- April 2019 (1)
- February 2019 (1)
- January 2019 (1)
- December 2018 (1)
- November 2018 (2)
- August 2018 (3)
- July 2018 (4)
- June 2018 (2)
- April 2018 (2)
- March 2018 (2)
- February 2018 (2)
- January 2018 (3)
- December 2017 (1)
- September 2017 (1)
- May 2017 (2)
- April 2017 (5)
- March 2017 (4)
- February 2017 (1)
- January 2017 (1)
- December 2016 (1)
- November 2016 (1)
- October 2016 (2)
- September 2016 (1)
- August 2016 (3)
- July 2016 (2)
- June 2016 (3)
- May 2016 (7)
- April 2016 (8)
- March 2016 (1)
- February 2016 (3)
- January 2016 (12)
- December 2015 (7)
- November 2015 (6)
- October 2015 (6)
- September 2015 (2)
- August 2015 (4)
- July 2015 (2)
- June 2015 (2)
- May 2015 (1)
- April 2015 (5)
- March 2015 (3)
- February 2015 (4)
- January 2015 (2)
- October 2014 (5)
- September 2014 (8)
- August 2014 (5)
- July 2014 (8)
- June 2014 (5)
- May 2014 (5)
- April 2014 (9)
- March 2014 (7)
- February 2014 (7)
- January 2014 (5)
- December 2013 (5)
- October 2013 (7)
- September 2013 (2)