Looking for NovaBACKUP? Visit NovaBACKUP.com
NovaStor offers all-inclusive pricing based on the volume of data you select to backup with unlimited servers and full application and hardware support.
To request pricing based on your specific IT environment and backup volume requirements, request a quote.
Try before you buy. Our backup experts are available to help you test our software in your environment through our complementary setup assistance.
Wir überprüfen und optimieren Ihre Datensicherung nach IT-Umstellungen oder für Unternehmensprüfungen.
Unsere Backup-Experten beraten Sie mit Know-how und langjähriger Erfahrung und liefern individuelle Lösungen.
In bewährten Schulungsformaten erwerben und erproben Sie die Fachkenntnisse für Ihren Backup- und Restore-Erfolg.
NovaStor backup experts share their extensive experience and know-how through whitepapers.
View our case studies for references and to learn about some of our customer successes.
Get detailed technical documentation for NovaStor products.
View our videos for step-by-step tutorials of NovaStor DataCenter software.
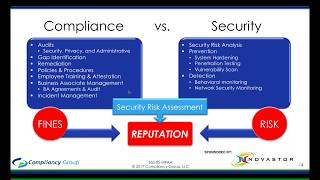
Gain valuable knowledge, insight and technical guidance by viewing our webinars.
Our certifications ensure that our products meet rigorous standards.